马上注册,结交更多好友,享用更多功能,让你轻松玩转社区。
您需要 登录 才可以下载或查看,没有账号?立即注册
×
1.认证流程分析
Spring Security中默认的一套登录流程是非常完善并且严谨的。但是项目需求非常多样化, 很多时候,我们可能还需要对Spring Secinity登录流程进行定制,定制的前提是开发者先深刻理解Spring Security登录流程,然后在此基础之上,完成对登录流程的定制。本文将从头梳理 Spring Security登录流程,并通过几个常见的登录定制案例,深刻地理解Spring Security登录流程。
本章涉及的主要知识点有:
- 登录流程分析。
- 配置多个数据源。
- 添加登录验证码。
1.1登录流程分析
要搞清楚Spring Security认证流程,我们得先认识与之相关的三个基本组件(Authentication 对象在前面文章种己经做过介绍,这里不再赘述):AuthenticationManager、ProviderManager以及AuthenticationProvider,同时还要去了解接入认证功能的过滤器 AbstractAuthenticationProcessingFilter,这四个类搞明白了,基本上认证流程也就清楚了,下面我们逐个分析一下。
1.1.1 AuthenticationManager
从名称上可以看出,AuthenticationManager是一个认证管理器,它定义了 Spring Security 过滤器要如何执行认证操作。AuthenticationManager在认证成功后,会返回一个Authentication对象,这个Authentication对象会被设置到SecurityContextHolder中。如果开发者不想用Spring Security提供的一套认证机制,那么也可以自定义认证流程,认证成功后,手动将Authentication 存入 SecurityContextHolder 中。- public interface AuthenticationManager {
- Authentication authenticate(Authentication var1) throws AuthenticationException;
- }
1.1.2 AuthenticationProvider
Spring Security支持多种不同的认证方式,不同的认证方式对应不同的身份 类型,AuthenticationProvider就是针对不同的身份类型执行具体的身份认证。例如,常见的 DaoAuthenticationProvider 用来支持用户名/密码登录认证,RememberMeAuthenticationProvider 用来支持“记住我”的认证。- public interface AuthenticationProvider {
- Authentication authenticate(Authentication var1) throws AuthenticationException;
- boolean supports(Class<?> var1);
- }
- authenticate方法用来执行具体的身份忧证。
- supports方法用来判断当前AuthenticationProvider是否支持对应的身份类型。
当使用用户名/密码的方式登录时,对应的AuthenticationProvider实现类是 DaoAuthenticationProvider , 而 DaoAuthenticationProvider 继承自 AbstractUserDetailsAuthenticationProvider并且没有重写authenticate方法,所以具体的认证逻辑在AbstractUserDetailsAuthenticationProvider 的 authenticate 方法中。我们就从 AbstractUserDetailsAuthenticationProvider开始看起:
查看代码- public abstract class AbstractUserDetailsAuthenticationProvider implements AuthenticationProvider, InitializingBean, MessageSourceAware {
- protected final Log logger = LogFactory.getLog(this.getClass());
- protected MessageSourceAccessor messages = SpringSecurityMessageSource.getAccessor();
- private UserCache userCache = new NullUserCache();
- private boolean forcePrincipalAsString = false;
- protected boolean hideUserNotFoundExceptions = true;
- private UserDetailsChecker preAuthenticationChecks = new AbstractUserDetailsAuthenticationProvider.DefaultPreAuthenticationChecks();
- private UserDetailsChecker postAuthenticationChecks = new AbstractUserDetailsAuthenticationProvider.DefaultPostAuthenticationChecks();
- private GrantedAuthoritiesMapper authoritiesMapper = new NullAuthoritiesMapper();
- public AbstractUserDetailsAuthenticationProvider() {
- }
- protected abstract void additionalAuthenticationChecks(UserDetails var1, UsernamePasswordAuthenticationToken var2) throws AuthenticationException;
- public final void afterPropertiesSet() throws Exception {
- Assert.notNull(this.userCache, "A user cache must be set");
- Assert.notNull(this.messages, "A message source must be set");
- this.doAfterPropertiesSet();
- }
- public Authentication authenticate(Authentication authentication) throws AuthenticationException {
- Assert.isInstanceOf(UsernamePasswordAuthenticationToken.class, authentication, () -> {
- return this.messages.getMessage("AbstractUserDetailsAuthenticationProvider.onlySupports", "Only UsernamePasswordAuthenticationToken is supported");
- });
- String username = authentication.getPrincipal() == null ? "NONE_PROVIDED" : authentication.getName();
- boolean cacheWasUsed = true;
- UserDetails user = this.userCache.getUserFromCache(username);
- if (user == null) {
- cacheWasUsed = false;
- try {
- user = this.retrieveUser(username, (UsernamePasswordAuthenticationToken)authentication);
- } catch (UsernameNotFoundException var6) {
- this.logger.debug("User '" + username + "' not found");
- if (this.hideUserNotFoundExceptions) {
- throw new BadCredentialsException(this.messages.getMessage("AbstractUserDetailsAuthenticationProvider.badCredentials", "Bad credentials"));
- }
- throw var6;
- }
- Assert.notNull(user, "retrieveUser returned null - a violation of the interface contract");
- }
- try {
- this.preAuthenticationChecks.check(user);
- this.additionalAuthenticationChecks(user, (UsernamePasswordAuthenticationToken)authentication);
- } catch (AuthenticationException var7) {
- if (!cacheWasUsed) {
- throw var7;
- }
- cacheWasUsed = false;
- user = this.retrieveUser(username, (UsernamePasswordAuthenticationToken)authentication);
- this.preAuthenticationChecks.check(user);
- this.additionalAuthenticationChecks(user, (UsernamePasswordAuthenticationToken)authentication);
- }
- this.postAuthenticationChecks.check(user);
- if (!cacheWasUsed) {
- this.userCache.putUserInCache(user);
- }
- Object principalToReturn = user;
- if (this.forcePrincipalAsString) {
- principalToReturn = user.getUsername();
- }
- return this.createSuccessAuthentication(principalToReturn, authentication, user);
- }
- protected Authentication createSuccessAuthentication(Object principal, Authentication authentication, UserDetails user) {
- UsernamePasswordAuthenticationToken result = new UsernamePasswordAuthenticationToken(principal, authentication.getCredentials(), this.authoritiesMapper.mapAuthorities(user.getAuthorities()));
- result.setDetails(authentication.getDetails());
- return result;
- }
- protected void doAfterPropertiesSet() throws Exception {
- }
- public UserCache getUserCache() {
- return this.userCache;
- }
- public boolean isForcePrincipalAsString() {
- return this.forcePrincipalAsString;
- }
- public boolean isHideUserNotFoundExceptions() {
- return this.hideUserNotFoundExceptions;
- }
- protected abstract UserDetails retrieveUser(String var1, UsernamePasswordAuthenticationToken var2) throws AuthenticationException;
- public void setForcePrincipalAsString(boolean forcePrincipalAsString) {
- this.forcePrincipalAsString = forcePrincipalAsString;
- }
- public void setHideUserNotFoundExceptions(boolean hideUserNotFoundExceptions) {
- this.hideUserNotFoundExceptions = hideUserNotFoundExceptions;
- }
- public void setMessageSource(MessageSource messageSource) {
- this.messages = new MessageSourceAccessor(messageSource);
- }
- public void setUserCache(UserCache userCache) {
- this.userCache = userCache;
- }
- public boolean supports(Class<?> authentication) {
- return UsernamePasswordAuthenticationToken.class.isAssignableFrom(authentication);
- }
- protected UserDetailsChecker getPreAuthenticationChecks() {
- return this.preAuthenticationChecks;
- }
- public void setPreAuthenticationChecks(UserDetailsChecker preAuthenticationChecks) {
- this.preAuthenticationChecks = preAuthenticationChecks;
- }
- protected UserDetailsChecker getPostAuthenticationChecks() {
- return this.postAuthenticationChecks;
- }
- public void setPostAuthenticationChecks(UserDetailsChecker postAuthenticationChecks) {
- this.postAuthenticationChecks = postAuthenticationChecks;
- }
- public void setAuthoritiesMapper(GrantedAuthoritiesMapper authoritiesMapper) {
- this.authoritiesMapper = authoritiesMapper;
- }
- private class DefaultPostAuthenticationChecks implements UserDetailsChecker {
- private DefaultPostAuthenticationChecks() {
- }
- public void check(UserDetails user) {
- if (!user.isCredentialsNonExpired()) {
- AbstractUserDetailsAuthenticationProvider.this.logger.debug("User account credentials have expired");
- throw new CredentialsExpiredException(AbstractUserDetailsAuthenticationProvider.this.messages.getMessage("AbstractUserDetailsAuthenticationProvider.credentialsExpired", "User credentials have expired"));
- }
- }
- }
- private class DefaultPreAuthenticationChecks implements UserDetailsChecker {
- private DefaultPreAuthenticationChecks() {
- }
- public void check(UserDetails user) {
- if (!user.isAccountNonLocked()) {
- AbstractUserDetailsAuthenticationProvider.this.logger.debug("User account is locked");
- throw new LockedException(AbstractUserDetailsAuthenticationProvider.this.messages.getMessage("AbstractUserDetailsAuthenticationProvider.locked", "User account is locked"));
- } else if (!user.isEnabled()) {
- AbstractUserDetailsAuthenticationProvider.this.logger.debug("User account is disabled");
- throw new DisabledException(AbstractUserDetailsAuthenticationProvider.this.messages.getMessage("AbstractUserDetailsAuthenticationProvider.disabled", "User is disabled"));
- } else if (!user.isAccountNonExpired()) {
- AbstractUserDetailsAuthenticationProvider.this.logger.debug("User account is expired");
- throw new AccountExpiredException(AbstractUserDetailsAuthenticationProvider.this.messages.getMessage("AbstractUserDetailsAuthenticationProvider.expired", "User account has expired"));
- }
- }
- }
- }
- 一开始先声明一个用户缓存对象userCache,默认情况下没有启用缓存对象。
- hideUserNotFoundExceptions表示是否隐藏用户名查找失败的异常,默认为true,为了确保系统安全,用户在登录失败时只会给出一个模糊提示,例如“用户名或密码输入错误“ 在Spring Security内部,如果用户名查找失败,则会抛出UsernameNotFoundException异常, 但是该异常会被自动隐藏,转而通过一个BadCredentialsException异常来代替它,这样,开发者在处理登录失败异常时,无论是用户名输入错误还是密码输入错误,收到的总是 BadCredentialsException,这样做的一个好处是可以避免新手程序员将用户名输入错误和密码输入错误两个异常分开提示。
- forcePrincipalAsString表示是否强制将Principal对象当成字符串来处理,默认是falser,Authentication中的Principal属性类型是一个Object,正常来说,通过Principal属性可以获取到当前登录用户对象(即UserDetails),但是如果forcePrincipalAsString设置为true,则 Authentication中的Principal属性返回就是当前登录用户名,而不是用户对象。
- preAuthenticationChecks对象则是用于做用户状态检査,在用户认证过程中,需要检验用户状态是否正常,例如账户是否被锁定、账户是否可用、账户是否过期等。
- postAuthenticationChecks对象主要负责在密码校验成功后,检査密码是否过期。
- additionalAuthenticationChecks是一个抽象方法,主要就是校验密码,具体的实现在 DaoAuthenticationProvider 中。
- authenticate方法就是核心的校验方法了。在方法中,首先从登录数据中获取用户名, 然后根据用户名去缓存中查询用户对象,如果査询不到,则根据用户名调用retrieveUser方法从数据库中加载用户;如果没有加载到用户,则抛出异常(用户不存在异常会被隐藏)。拿到用户对象之后,首先调用check方法进行用户状态检査,然后调用 additionalAuthenticationChecks 方法进行密码的校验操作,最后调用 postAuthenticationChecks.check方法检査密码是否过期,当所有步骤都顺利完成后,调用createSuccessAuthentication 方法创建一个认证后的 UsernamePasswordAuthenticationToken 对象并返回,认证后的对象中包含了认证主体、凭证以及角色等信息。
这就是 AbstractUserDetailsAuthenticationProvider类的工作流程,有几个抽象方法是在 DaoAuthenticationProvider 中实现的,我们再来看一下 DaoAuthenticationProvider中的定义:
查看代码- public class DaoAuthenticationProvider extends AbstractUserDetailsAuthenticationProvider {
- private static final String USER_NOT_FOUND_PASSWORD = "userNotFoundPassword";
- private PasswordEncoder passwordEncoder;
- private volatile String userNotFoundEncodedPassword;
- private UserDetailsService userDetailsService;
- private UserDetailsPasswordService userDetailsPasswordService;
- public DaoAuthenticationProvider() {
- this.setPasswordEncoder(PasswordEncoderFactories.createDelegatingPasswordEncoder());
- }
- protected void additionalAuthenticationChecks(UserDetails userDetails, UsernamePasswordAuthenticationToken authentication) throws AuthenticationException {
- if (authentication.getCredentials() == null) {
- this.logger.debug("Authentication failed: no credentials provided");
- throw new BadCredentialsException(this.messages.getMessage("AbstractUserDetailsAuthenticationProvider.badCredentials", "Bad credentials"));
- } else {
- String presentedPassword = authentication.getCredentials().toString();
- if (!this.passwordEncoder.matches(presentedPassword, userDetails.getPassword())) {
- this.logger.debug("Authentication failed: password does not match stored value");
- throw new BadCredentialsException(this.messages.getMessage("AbstractUserDetailsAuthenticationProvider.badCredentials", "Bad credentials"));
- }
- }
- }
- protected void doAfterPropertiesSet() {
- Assert.notNull(this.userDetailsService, "A UserDetailsService must be set");
- }
- protected final UserDetails retrieveUser(String username, UsernamePasswordAuthenticationToken authentication) throws AuthenticationException {
- this.prepareTimingAttackProtection();
- try {
- UserDetails loadedUser = this.getUserDetailsService().loadUserByUsername(username);
- if (loadedUser == null) {
- throw new InternalAuthenticationServiceException("UserDetailsService returned null, which is an interface contract violation");
- } else {
- return loadedUser;
- }
- } catch (UsernameNotFoundException var4) {
- this.mitigateAgainstTimingAttack(authentication);
- throw var4;
- } catch (InternalAuthenticationServiceException var5) {
- throw var5;
- } catch (Exception var6) {
- throw new InternalAuthenticationServiceException(var6.getMessage(), var6);
- }
- }
- protected Authentication createSuccessAuthentication(Object principal, Authentication authentication, UserDetails user) {
- boolean upgradeEncoding = this.userDetailsPasswordService != null && this.passwordEncoder.upgradeEncoding(user.getPassword());
- if (upgradeEncoding) {
- String presentedPassword = authentication.getCredentials().toString();
- String newPassword = this.passwordEncoder.encode(presentedPassword);
- user = this.userDetailsPasswordService.updatePassword(user, newPassword);
- }
- return super.createSuccessAuthentication(principal, authentication, user);
- }
- private void prepareTimingAttackProtection() {
- if (this.userNotFoundEncodedPassword == null) {
- this.userNotFoundEncodedPassword = this.passwordEncoder.encode("userNotFoundPassword");
- }
- }
- private void mitigateAgainstTimingAttack(UsernamePasswordAuthenticationToken authentication) {
- if (authentication.getCredentials() != null) {
- String presentedPassword = authentication.getCredentials().toString();
- this.passwordEncoder.matches(presentedPassword, this.userNotFoundEncodedPassword);
- }
- }
- public void setPasswordEncoder(PasswordEncoder passwordEncoder) {
- Assert.notNull(passwordEncoder, "passwordEncoder cannot be null");
- this.passwordEncoder = passwordEncoder;
- this.userNotFoundEncodedPassword = null;
- }
- protected PasswordEncoder getPasswordEncoder() {
- return this.passwordEncoder;
- }
- public void setUserDetailsService(UserDetailsService userDetailsService) {
- this.userDetailsService = userDetailsService;
- }
- protected UserDetailsService getUserDetailsService() {
- return this.userDetailsService;
- }
- public void setUserDetailsPasswordService(UserDetailsPasswordService userDetailsPasswordService) {
- this.userDetailsPasswordService = userDetailsPasswordService;
- }
- }
- 首先定义了 USER_NOT_FOUND_PASSWORD常量,这个是当用户查找失败时的默认密码;passwordEncoder是一个密码加密和比对工具,这个在后面会有专门的介绍,这里先不做过多解释;userNotFoundEncodedPassword变量则用来保存默认密码加密后的值; userDetailsService是一个用户查找工具,userDetailsService在前面己经讲过,这里不再赘述; userDetailsPasswordService则用来提供密码修改服务。
- 在DaoAuthenticationProvider的构造方法中,默认就会指定PasswordEncoder,当然开发者也可以通过set方法自定义PasswordEncoder。
- additionalAuthenticationchecks方法主要进行密码校验,该方法第一个参数userDetails 是从数据库中查询出来的用户对象,第二个参数authentication则是登录用户输入的参数。从这两个参数中分别提取出来用户密码,然后调用passwordEncoder.matches方法进行密码比对。
- retrieveUser方法则是获取用户对象的方法,具体做法就是调用 UserDetailsService#loadUserByUsername 方法去数据库中查询。
- 在retrieveUser方法中,有一个值得关注的地方。在该方法一开始,首先会调用 prepareTimingAttackProtection 方法,该方法的作用是使用 PasswordEncoder 对常量 USER_NOT_FOUND_PASSWORD 进行加密,将加密结果保存在 userNotFoundEncodedPassword变量中。当根据用户名查找用户时,如果抛出了 UsernameNotFoundException异常, 则调用mitigateAgainstTimingAttack方法进行密码比对由有读者会说,用户都没查找到,怎么 比对密码?需要注意,在调用mitigateAgainstTimingAttack方法进行密码比对时,使用了 userNotFoundEncodedPassword变量作为默认密码和登录请求传来的用户密码进行比对,这是 一个一开始就注定要失败的密码比对,那么为什么还要进行比对呢?这主要是为了避免旁道攻击(Side-channel attack)。如果根据用户名査找用户失败,就直接抛出异常而不进行密码比对, 那么黑客经过大量的测试,就会发现有的请求耗费时间明显小于其他请求,那么进而可以得出该请求的用户名是一个不存在的用户名(因为用户名不存在,所以不需要密码比对,进而节省时间),这样就可以获取到系统信息。为了避免这一问题,所以当用户查找失败时,也会调用 mitigateAgainstTimingAttack方法进行密码比对,这样就可以迷惑黑客。
- createSuccessAuthentication方法则是在登录成功后,创建一个全新的 UsernamePasswordAuthenticationToken对象,同时会判断是否需要进行密码升级,如果需要进行密码升级,就会在该方法中进行加密方案升級。通过对 AbstractUserDetailsAuthenticationProvider 和 DaoAuthenticationProvider 的讲解,相信你己经很明白AuthenticationProvider中的认证逻辑了。
在密码学中,旁道攻击(Side-channel attack )又称侧信道攻击、边信道攻击。这种攻击方式不是暴力破解或者是研究加密算法的弱点。它是基于从密码系统的物理实现中获取信息, 比如时间、功率消耗、电磁泄漏等,这些信息可被利用于对系统的进一步破解。
1.1.3 ProviderManager
ProviderManager是AuthenticationManager的一个重要实现类,正在开始学习之前,我们先通过一幅图来了解一下ProviderManager和AuthenticationProvider之间的关系,如图3-1所示。
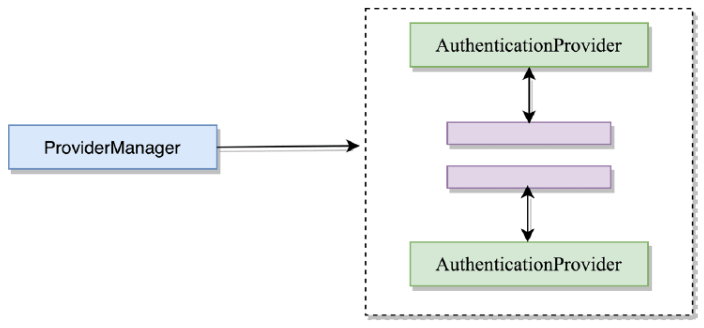
图 3-1
在Spring Security中,由于系统可能同时支持多种不同的认证方式,例如同时支持用户名 /密码认证、RememberMe认证、手机号码动态认证等,而不同的认证方式对应了不同的 AuthenticationProvider,所以一个完整的认证流程可能由多个AuthenticationProvider来提供。
多个AuthenticationProvider将组成一个列表,这个列表将由ProviderManager代理。换句话说,在 ProviderManager 中存在一个 AuthenticationProvider 列表,在 ProviderManager 中遍历列表中的每一个AuthenticationProvider去执行身份认证,最终得到认证结果。
ProviderManager 本身也可以再配置一个 AuthenticationManager 作为 parent,这样当 ProviderManager认证失败之后,就可以进入到parent中再次进行认证。理论上来说, ProviderManager的parent可以是任意类型的 AuthenticationManager,但是通常都是由 ProviderManager 来扮演 parent 的角色,也就是 ProviderManager 是 ProviderManager 的 parent。
ProviderManager本身也可以有多个,多个ProviderManager共用同一个parent,当存在多个过滤器链的时候非常有用。当存在多个过滤器链时,不同的路径可能对应不同的认证方式, 但是不同路径可能又会同时存在一些共有的认证方式,这些共有的认证方式可以在parent中统 一处理。
根据上面的介绍,图 3-2是ProviderManager和AuthenticationProvider关系图。
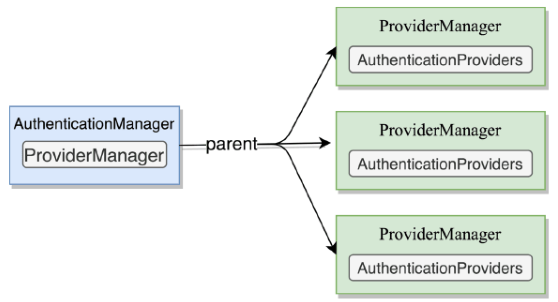
图 3-2
我们重点看一下ProviderManager中的authenticate方法:
查看代码- public Authentication authenticate(Authentication authentication) throws AuthenticationException {
- Class<? extends Authentication> toTest = authentication.getClass();
- AuthenticationException lastException = null;
- AuthenticationException parentException = null;
- Authentication result = null;
- Authentication parentResult = null;
- boolean debug = logger.isDebugEnabled();
- Iterator var8 = this.getProviders().iterator();
- while(var8.hasNext()) {
- AuthenticationProvider provider = (AuthenticationProvider)var8.next();
- if (provider.supports(toTest)) {
- if (debug) {
- logger.debug("Authentication attempt using " + provider.getClass().getName());
- }
- try {
- result = provider.authenticate(authentication);
- if (result != null) {
- this.copyDetails(authentication, result);
- break;
- }
- } catch (InternalAuthenticationServiceException | AccountStatusException var13) {
- this.prepareException(var13, authentication);
- throw var13;
- } catch (AuthenticationException var14) {
- lastException = var14;
- }
- }
- }
- if (result == null && this.parent != null) {
- try {
- result = parentResult = this.parent.authenticate(authentication);
- } catch (ProviderNotFoundException var11) {
- } catch (AuthenticationException var12) {
- parentException = var12;
- lastException = var12;
- }
- }
- if (result != null) {
- if (this.eraseCredentialsAfterAuthentication && result instanceof CredentialsContainer) {
- ((CredentialsContainer)result).eraseCredentials();
- }
- if (parentResult == null) {
- this.eventPublisher.publishAuthenticationSuccess(result);
- }
- return result;
- } else {
- if (lastException == null) {
- lastException = new ProviderNotFoundException(this.messages.getMessage("ProviderManager.providerNotFound", new Object[]{toTest.getName()}, "No AuthenticationProvider found for {0}"));
- }
- if (parentException == null) {
- this.prepareException((AuthenticationException)lastException, authentication);
- }
- throw lastException;
- }
- }
- 首先通过requiresAuthentication方法来判断当前请求是不是登录认证请求,如果是认证请求,就执行接下来的认证代码;如果不是认证请求,则直接继续走剩余的过滤器即可。
- 调用attemptAuthentication方法来获取一个经过认证后的Authentication对象, attemptAuthentication方法是一个抽象方法,具体实现在它的子类 UsernamePasswordAuthenticationFilter 中。
- 认证成功后,通过sessionStrategy.onAuthentication方法来处理session并发问题。
- continueChainBeforeSuccessfulAuthentication变量用来判断请求是否还需要继续向下走,默认情况下该参数的值为false,即认证成功后,后续的过滤器将不再执行了。
- unsuccessfulAuthentication方法用来处理认证失败事宜,主要做了三件事:①从 SecurityContextHolder中清除数据;②清除Cookie等信息;③调用认证失败的回调方法。
- successfulAuthentication方法主要用来处理认证成功事宜,主要做了四件事:①向 SecurityContextHolder中存入用户信息;②处理Cookie;③发布认证成功事件,这个事件类型 InteractiveAuthenticationSuccessEvent,表示通过一些自动交互的方式认证成功,例如通过 RememberMe的方式登录;④调用认证成功的回调方法。
这就是 AbstractAuthenticationProcessingFilter大致上所做的事情,还有一个抽象方法 attemptAuthentication 是在它的继承类 UsernamePasswordAuthenticationFilter中实现的,接下来我们来看—下UsernamePasswordAuthenticationFilter类:
查看代码- public abstract class AbstractAuthenticationProcessingFilter extends GenericFilterBean
- implements ApplicationEventPublisherAware, MessageSourceAware {
- protected ApplicationEventPublisher eventPublisher;
- protected AuthenticationDetailsSource<HttpServletRequest, ?> authenticationDetailsSource = new WebAuthenticationDetailsSource();
- private AuthenticationManager authenticationManager;
- protected MessageSourceAccessor messages = SpringSecurityMessageSource.getAccessor();
- private RememberMeServices rememberMeServices = new NullRememberMeServices();
- private RequestMatcher requiresAuthenticationRequestMatcher;
- private boolean continueChainBeforeSuccessfulAuthentication = false;
- private SessionAuthenticationStrategy sessionStrategy = new NullAuthenticatedSessionStrategy();
- private boolean allowSessionCreation = true;
- private AuthenticationSuccessHandler successHandler = new SavedRequestAwareAuthenticationSuccessHandler();
- private AuthenticationFailureHandler failureHandler = new SimpleUrlAuthenticationFailureHandler();
- protected AbstractAuthenticationProcessingFilter(String defaultFilterProcessesUrl) {
- setFilterProcessesUrl(defaultFilterProcessesUrl);
- }
- protected AbstractAuthenticationProcessingFilter(
- RequestMatcher requiresAuthenticationRequestMatcher) {
- Assert.notNull(requiresAuthenticationRequestMatcher,
- "requiresAuthenticationRequestMatcher cannot be null");
- this.requiresAuthenticationRequestMatcher = requiresAuthenticationRequestMatcher;
- }
- @Override
- public void afterPropertiesSet() {
- Assert.notNull(authenticationManager, "authenticationManager must be specified");
- }
- public void doFilter(ServletRequest req, ServletResponse res, FilterChain chain)
- throws IOException, ServletException {
- HttpServletRequest request = (HttpServletRequest) req;
- HttpServletResponse response = (HttpServletResponse) res;
- if (!requiresAuthentication(request, response)) {
- chain.doFilter(request, response);
- return;
- }
- if (logger.isDebugEnabled()) {
- logger.debug("Request is to process authentication");
- }
- Authentication authResult;
- try {
- authResult = attemptAuthentication(request, response);
- if (authResult == null) {
- return;
- }
- sessionStrategy.onAuthentication(authResult, request, response);
- }
- catch (InternalAuthenticationServiceException failed) {
- logger.error(
- "An internal error occurred while trying to authenticate the user.",
- failed);
- unsuccessfulAuthentication(request, response, failed);
- return;
- }
- catch (AuthenticationException failed) {
- unsuccessfulAuthentication(request, response, failed);
- return;
- }
- if (continueChainBeforeSuccessfulAuthentication) {
- chain.doFilter(request, response);
- }
- successfulAuthentication(request, response, chain, authResult);
- }
- protected boolean requiresAuthentication(HttpServletRequest request,
- HttpServletResponse response) {
- return requiresAuthenticationRequestMatcher.matches(request);
- }
- public abstract Authentication attemptAuthentication(HttpServletRequest request,
- HttpServletResponse response) throws AuthenticationException, IOException,
- ServletException;
- protected void successfulAuthentication(HttpServletRequest request,
- HttpServletResponse response, FilterChain chain, Authentication authResult)
- throws IOException, ServletException {
- if (logger.isDebugEnabled()) {
- logger.debug("Authentication success. Updating SecurityContextHolder to contain: "
- + authResult);
- }
- SecurityContextHolder.getContext().setAuthentication(authResult);
- rememberMeServices.loginSuccess(request, response, authResult);
- if (this.eventPublisher != null) {
- eventPublisher.publishEvent(new InteractiveAuthenticationSuccessEvent(
- authResult, this.getClass()));
- }
- successHandler.onAuthenticationSuccess(request, response, authResult);
- }
- protected void unsuccessfulAuthentication(HttpServletRequest request,
- HttpServletResponse response, AuthenticationException failed)
- throws IOException, ServletException {
- SecurityContextHolder.clearContext();
- if (logger.isDebugEnabled()) {
- logger.debug("Authentication request failed: " + failed.toString(), failed);
- logger.debug("Updated SecurityContextHolder to contain null Authentication");
- logger.debug("Delegating to authentication failure handler " + failureHandler);
- }
- rememberMeServices.loginFail(request, response);
- failureHandler.onAuthenticationFailure(request, response, failed);
- }
- }
- 首先声明了默认情况下登录表单的用户名字段和密码字段,用户名字段的key默认是username,密码字段的key默认是password。当然,这两个字段也可以自定义,自定义的方式就是我们在 SecurityConfig 中配置的 .usernameParameter("uname")和 .passwordParameter("passwd")(参考前几节)
- 在UsernamePasswordAuthenticationFilter过滤器构建的时候,指定了当前过滤器只用来处理登录请求,默认的登录请求是/login,当然开发者也可以自行配置。
- 接下来就是最重要的attemptAuthentication方法了,在该方法中,首先确认请求是 post类型;然后通过obtainUsername和obtainPassword方法分别从请求中提取出用户名和密码, 具体的提取过程就是调用request.getParameter方法;拿到登录请求传来的用户名/密码之后, 构造出一个 authRequest,然后调用 getAuthenticationManager().authenticate 方法进行认证,这就进入到我们前面所说的ProviderManager的流程中了,具体认证过程就不再赘述了。
以上就是整个认证流程。
搞懂了认证流程,那么接下来如果想要自定义一些认证方式,就会非常容易了,比如定义多个数据源、添加登录校验码等。下面,我们将通过两个案例,来活学活用上面所讲的认证流程。
免责声明:如果侵犯了您的权益,请联系站长,我们会及时删除侵权内容,谢谢合作! |